Amazing,100% candidates have passed the 70-410 exam by practising the preparation material of GreatExam, because the braindumps are the latest and cover every aspect of 70-410 exam. Download the braindumps for an undeniable success in 70-410 exam.
QUESTION 151
Your network contains an Active Directory domain named contoso.com.
All client computer accounts are in an organizational unit (OU) named AllComputers.
Client computers run either Windows 7 or Windows 8.
You create a Group Policy object (GPO) named GP1.
You link GP1 to the AllComputers OU.
You need to ensure that GP1 applies only to computers that have more than 8 GB of memory.
What should you configure?
A. The Security settings of AllComputers
B. The Security settings of GP1
C. The WMI filter for GP1
D. The Block Inheritance option for AllComputers
Answer: C
Explanation:
Windows Management Instrumentation (WMI) filters allow you to dynamically determine the scope of Group Policy objects (GPOs) based on attributes of the target computer.
When a GPO that is linked to a WMI filter is applied on the target computer, the filter is evaluated on the target computer. If the WMI filter evaluates to false, the GPO is not applied (except if the client computer is running Windows Server, in which case the filter is ignored and the GPO is always applied). If the WMI filter evaluates to true, the GPO is applied. WMI filters, like GPOs, are stored on a per-domain basis. A WMI filter and the GPO it is linked to must be in the same domain.
SELECT Total Physical Memory FROM Win32_ComputerSystem WHERE
TotalPhysicalMemory >= 8000000000
QUESTION 152
Your network contains an Active Directory domain named contoso.com.
The domain contains two servers named Server1 and Server2.
Server1 runs Windows Server 2012 R2. Server2 runs Windows Server 2008 R2 Service Pack 1 (SP1) and has the DHCP Server server role installed.
You need to manage DHCP on Server2 by using the DHCP console on Server1.
What should you do first?
A. From Windows Firewall with Advanced Security on Server2, create an inbound rule.
B. From Internet Explorer on Server2, download and install Windows Management Framework 3.0.
C. From Server Manager on Server1, install a feature.
D. From Windows PowerShell on Server2, run Enable PSRemoting.
Answer: C
Explanation:
When the DHCP role is installed, it appears that the firewall rules are automatically added. This means you only need to add the DHCP Manager MMC snap-in which is a Role Administration Tool feature.
QUESTION 153
Your network contains an Active Directory domain named contoso.com. The domain contains a member server named HVServer1. HVServer1 runs Windows Server 2012 and has the Hyper-V server role installed. HVServer1 hosts 10 virtual machines. All of the virtual machines connect to a virtual switch named Switch1. Switch1 is configured as a private network. All of the virtual machines have the DHCP guard and the router guard settings enabled.
You install the DHCP server role on a virtual machine named Server 1.
You authorize Server1 as a DHCP server in contoso.com.
You create an IP scope.
You discover that the virtual machines connected to Switch1 do not receive IP settings from Server1.
You need to ensure that the virtual machines can use Server1 as a DHCP server.
What should you do?
A. Enable MAC address spoofing on Server1.
B. Disable the DHCP guard on all of the virtual machines that are DHCP clients.
C. Disable the DHCP guard on Server1.
D. Enable single-root I/O virtualization (SR-IOV) on Server1.
Answer: C
Explanation:
Private virtual networks are used where you want to allow communications between virtual machine to virtual machine on the same physical server In a block diagram, a private network is an internal network without a virtual NIC in the parentpartition. A private network would commonly be used where you need complete isolation of virtual machines from external and parent partition traffic. DMZ workloads running on a leg of a tri-homed firewall, or an isolated test domain are examples where this type of network may be useful.
DHCP Guard is a feature that you can use (as the owner of the hypervisor) to prevent VMs that you do not authorize from acting as DHCP Servers. Unauthorized and Authorized is a procedural / process phrase. It is not a technical phrase or any setting
that can be applied. It is the business decision to call machine authorized or not. DHCP Guard is specific to the port / vNIC of a VM. And the setting moves with the VM / vNIC.
DHCPGuard allows you to specify whether DHCP server messages coming from a VM should be dropped. For VMs that are running an authorized instance of the DHCP server role, you can turn DHCPGuard off by using the following cmdlet:
Set-VMNetworkAdapter – VMName MyDhcpServer1 – DhcpGuard Off
For all other VMs that are not authorized DHCP servers, you can prevent them from becoming a rogue
DHCP server by turning DHCPGuard on, using the following cmdlet.
Set-VMNetworkAdapter – VMName CustomerVM – DhcpGuard On
http://technet.microsoft.com/en-us/library/jj679878.aspx#bkmk_dhcp http://blogs.technet.com/b/jhoward/archive/2008/06/17/hyper-v-what-are-the-uses-for-different-types-of- virtual-networks.aspx
QUESTION 154
Hotspot Question
Your network contains an Active Directory domain named adatum.com.
You create an account for a temporary employee named User1.
You need to ensure that User1 can log on to the domain only between 08:00 and 18:00 from a client computer named Computer1.
From which tab should you perform the configuration? To answer, select the appropriate tab in the answer area.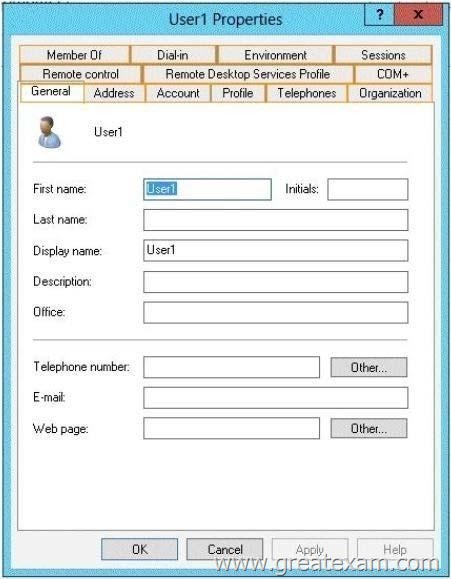
Answer: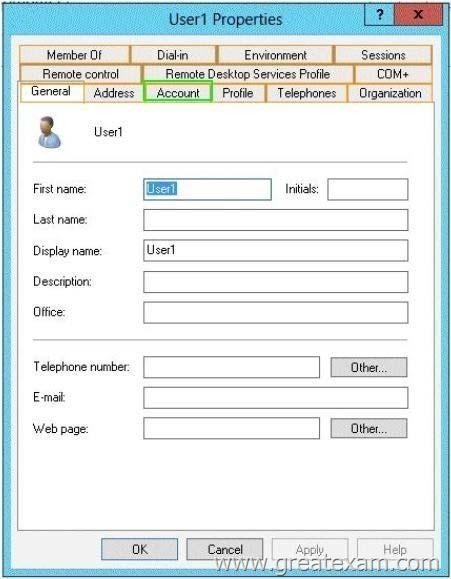
Explanation:
To set logon hours
1. Open Active Directory Users and Computers.
2. In the console tree, click Users.
Where?
Active Directory Users and Computers/domain
node/Users Or, click the folder that contains the user account.
3. Right-click the user account, and then click Properties.
4. On the Account tab, click Logon Hours, and then set the permitted or denied logon hours for the user.
http://technet.microsoft.com/en-us/library/cc740199(v=ws.10).aspx
QUESTION 155
You work as a senior administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers on the L2P.com network have Windows Server 2012 R2 installed.
You are running a training exercise for junior administrators.
You are currently discussing the new VHD format called VHDX.
Which of the following is TRUE with regards to VHDX? (Choose all that apply.)
A. It supports virtual hard disk storage capacity of up to 64 GB.
B. It supports virtual hard disk storage capacity of up to 64 TB.
C. It does not provide protection against data corruption during power failures.
D. It has the ability to store custom metadata about the file that the user might want to record.
Answer: BD
Explanation:
The main new features of the VHDX format are:
Support for virtual hard disk storage capacity of up to 64 TB.
Protection against data corruption during power failures by logging updates to the VHDX metadata structures. Improved alignment of the virtual hard disk format to work well on large sector disks.
The VHDX format also provides the following features:
Larger block sizes for dynamic and differencing disks, which allows these disks to attune to the needs of the workload.
A 4-KB logical sector virtual disk that allows for increased performance when used by applications and workloads that are designed for 4-KB sectors.
The ability to store custom metadata about the file that the user might want to record, such as operating system version or patches applied.
Efficiency in representing data (also known as “trim”), which results in smaller file size and allows the underlying physical storage device to reclaim unused space. (Trim requires physical disks directly attached to a virtual machine or SCSI disks, and trim-compatible hardware.)
VHDX Format – Features and Benefits
VHDX format features provide features at the virtual hard disk as well as virtual hard disk file layers and is optimized to work well with modern storage hardware configurations and capabilities. At the virtual hard disk layer, benefits include the ability to represent a large virtual disk size up to 64 TB, support larger logical sector sizes for a virtual disk up to 4 KB that facilitates the conversion of 4 KB sector physical disks to virtual disks, and support large block sizes for a virtual disk up to 256 MB that enables tuning block size to match the IO patterns of the application or system for optimal performance. At the virtual hard disk file layer, the benefits include the use of a log to ensure resiliency of the VHDX file to corruptions from system power failure events and a mechanism that allows for small pieces of user generated data to be transported along with the VHDX file. On modern storage platforms, the benefits include optimal performance on host disks that have physical sector sizes larger than 512 bytes through improved data alignment and capability to use the information from the UNMAP command, sent by the application or system using the virtual hard disk, to optimize the size of the VHDX file. The format is designed so that additional features could be introduced in the future by Microsoft or extended by other parser implementations. The format provides parsers the ability to detect features in a VHDX file that a parser does not understand.
http://technet.microsoft.com/en-us/library/hh831446.aspx
http://www.microsoft.com/en-us/download/details.aspx?id=34750
QUESTION 156
You have a server named Server1 that runs a Server Core Installation of Windows Server 2012 R2. You attach a 4-TB disk to Server1. The disk is configured as an MBR disk.
You need to ensure that you can create a 4-TB volume on the disk.
Which Diskpart command should you use?
A. Automount
B. Convert
C. Expand
D. Attach
Answer: B
Explanation:
You can use Diskpart to convert a basic disk to a dynamic disk. The basic disk can either be empty or containeither primary partitions or logical drives. The basic disk can be a data disk or system or boot drive. A MBR file structure is only capable of 2TB maximum. The disk will have to be converted to a GPT filestructure. GPT is capable of 18 exabytes volumes. Convert gpt – Converts an empty basic disk with the master boot record (MBR) partition style into a basic diskwith the GUID partition table (GPT) partition style. The disk may be a basic or a dynamic disk but it must not contain any valid data partitions or volumes.
http://technet.microsoft.com/en-us/library/cc766465(v=ws.10).aspx http://support.microsoft.com/kb/300415/en-us
QUESTION 157
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server1. Server1 runs Windows Server 2012 R2.
You need to create 3-TB virtual hard disk (VHD) on Server1.
Which tool should you use?
A. Server Manager
B. Diskpart
C. New-StoragePool
D. New-VirtualDisk
Answer: B
Explanation:
New-VirtualDisk – Creates a new virtual disk in the specified storage pool.
Although the new Server Manager UI in Windows Server 2012 R2 provides a very convenient and intuitive workflow to provision and manage Storage, interaction with PowerShell is required to access many of the advanced features.
If I then create a simple 200GB Virtual Disk via the UI named VDiskSimpleUI, the resulting Virtual Disk leverages 8 columns and maintains 1 copy of the data. But when creating the Virtual Disk via PowerShell,
I can force the tripping across all nine of the disks and optimize performance.
New-VirtualDisk -StoragePoolFriendlyName Pool01 – ResiliencySettingName Simple – Size 200GB – FriendlyName VDiskSimplePS – ProvisioningType Fixed – NumberOfDataCopies 1
– NumberOfColumns 9
And creating a mirrored 200GB Virtual Disk via the UI named VDiskMirrorUI produces a Virtual Disk with 4 columns and 2 data copies. But with PowerShell, I can create a slightly different configuration, increasing the data protection (and also the disk footprint):
New-VirtualDisk -StoragePoolFriendlyName Pool01 -ResiliencySettingName Mirror -Size 200GB –
FriendlyName VDiskMirrorPS -ProvisioningType Fixed -NumberOfDataCopies
3 -NumberOfColumns 3
http://blogs.technet.com/b/wincat/archive/2012/05/21/optimizing-windows-server-2012-storagemanagement-via-powershell-for-both-performance-and-resiliency.aspx
http://technet.microsoft.com/en-us/library/hh848643%28v=wps.620%29.aspx
QUESTION 158
Your network contains an Active Directory domain named contoso.com.
All domain controllers run Windows Server 2012 R2.
You create and enforce the default AppLocker executable rules.
Users report that they can no longer execute a legacy application installed in the root of drive C.
You need to ensure that the users can execute the legacy application.
What should you do?
A. Modify the action of the existing rules.
B. Create a new rule.
C. Add an exception to the existing rules.
D. Delete an existing rule.
Answer: B
Explanation:
AppLocker is a feature that advances the functionality of the Software Restriction Policies feature. AppLocker contains new capabilities and extensions that reduce administrative overhead and help administrators control how users can access and use files, such as executable files, scripts, Windows Installer files, and DLLs. By using AppLocker, you can:
Define rules based on file attributes that persist across application updates, such as the publisher name (derived from the digital signature), product name, file name, and file version. You can also create rules based on the file path and hash.
Assign a rule to a security group or an individual user.
Create exceptions to rules. For example, you can create a rule that allows all users to run all Windows binaries except the Registry Editor (Regedit.exe).
Use audit-only mode to deploy the policy and understand its impact before enforcing it. . Create rules on a staging server, test them, export them to your production environment, and then import them into a Group Policy Object.
Simplify creating and managing AppLocker rules by using Windows PowerShell cmdlets for AppLocker.
AppLocker default rules
AppLocker allows you to generate default rules for each of the rule types.
Executable default rule types:
Allow members of the local Administrators group to run all applications. Allow members of the Everyone group to run applications that are located in the Windows folder. Allow members of the Everyone group to run applications that are located in the Program Filesfolder. Windows Installer default rule types:
Allow members of the local Administrators group to run all Windows Installer files. Allow members of the Everyone group to run digitally signed Windows Installer files. Allow members of the Everyone group to run all Windows Installer files located in the Windows\Installer folder. Script default rule types:
Allow members of the local Administrators group to run all scripts. Allow members of the Everyone group to run scripts located in the Program Files folder. Allow members of the Everyone group to run scripts located in the Windows folder. DLL default rule types:( this on can affect system performance ) Allow members of the local Administrators group to run all DLLs. Allow members of the Everyone group to run DLLs located in the Program Files folder. Allow members of the Everyone group to run DLLs located in the Windows folder. You can apply AppLocker rules to individual users or to a group of users. If you apply a rule to a group of users, all users in that group are affected by that rule. If you need to allow a subset of a user group to use an application, you can create a special rule for that subset. For example, the rule “Allow Everyone to run Windows except Registry Editor” allows everyone in the organization to run the Windows operating system, but it does not allow anyone to run Registry Editor.
The effect of this rule would prevent users such as Help Desk personnel from running a program that is necessary for their support tasks. To resolve this problem, create a second rule that applies to the Help Desk user group: “Allow Help Desk to run Registry Editor.” If you create a deny rule that does not allow any users to run Registry Editor, the deny rule will override the second rule that allows the Help Desk user group to run Registry Editor.
http://technet.microsoft.com/library/hh831440.aspx
http://technet.microsoft.com/en-us/library/dd759068.aspx
http://technet.microsoft.com/de-de/library/hh994621.aspx
QUESTION 159
You have two servers named Server! and Server2. Both servers run Windows Server 2012 R2.
The servers are configured as shown in the following table.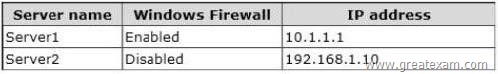
The routing table for Server1 is shown in the Routing Table exhibit. (Click the Exhibit button.)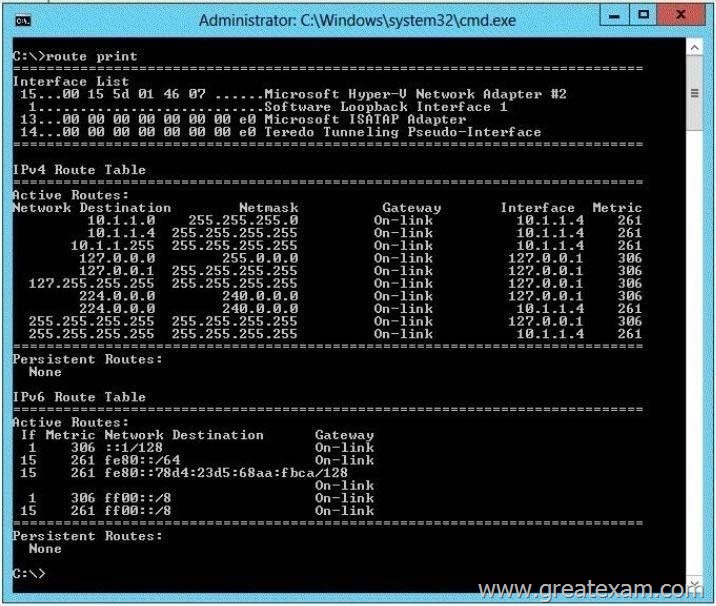
From Server1, you attempt to ping Server2, but you receive an error message as shown in the Error exhibit. (Click the Exhibit button.)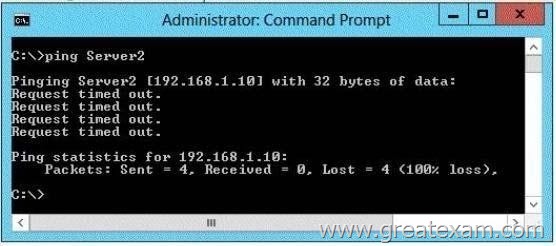
You need to ensure that you can successfully ping Server2 from Server1.
What should you do on Server1?
A. Disable Windows Firewall.
B. Modify the default gateway settings.
C. Modify the DNS settings.
D. Modify the subnet mask.
Answer: B
Explanation:
Route is used to view and modify the IP routing table.
Route Print displays a list of current routes that the host knows. Default gateways are important to make IP routing work efficiently. TCP/IP hosts rely on default gateways for most of their communication needs with hosts on remote networksegments. In this way, individual hosts are freed of the burden of having to maintain extensive andcontinuously updated knowledge about individual remote IP network segments. Only the router that acts as thedefault gateway needs to maintain this level of routing knowledge to reach other remote network segments inthe larger internetwork. In order for Host A on Network 1 to communicate with Host B on Network 2, Host A first checks its routing tableto see if a specific route to Host B exists. If there is no specific route to Host B, Host A forwards its TCP/IPtraffic for Host B to its own default gateway, IP Router 1.
http://technet.microsoft.com/en-us/library/cc779696%28v=ws.10%29.aspx http://technet.microsoft.com/en-us/library/cc958877.aspx
QUESTION 160
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. The domain contains a virtual machine named VM1.
A developer wants to attach a debugger to VM1.
You need to ensure that the developer can connect to VM1 by using a named pipe.
Which virtual machine setting should you configure?
A. Network Adapter
B. BIOS
C. Processor
D. COM 1
Answer: D
Explanation:
Named pipe. This option connects the virtual serial port to a Windows named pipe on the host operatingsystem or a computer on the network. A named pipe is a portion of memory that can be used by one processto pass information to another process, so that the output of one is the input of the other. The second processcan be local (on the same computer as the first) or remote (on a networked computer). For example, a localnamed pipe path could be \\.\pipe\mypipename. Named pipes can be used to create a virtual null modem cable between two virtual machines, or between avirtual machine and a debugging program on the host operating system that supports the use of named pipes.
By connecting two virtual serial ports to the same named pipe, you can create a virtual null modem cableconnection. Named pipes are useful for debugging or for any program that requires a null modem connection.
http://technet.microsoft.com/en-us/library/ee449417(v=ws.10).aspx http://blogs.msdn.com/b/ntdebugging/archive/2011/12/30/configuring-a-hyper-v-vm-forkernel- debugging.aspx
QUESTION 161
Your network contains an Active Directory domain named contoso.com.
Your company hires 500
temporary employees for the summer. The human resources department gives you a Microsoft Excel document that contains a list of the temporary employees.
You need to automate the creation of user accounts for the 500 temporary employees.
Which tool should you use?
A. The Add-Member cmdlet
B. ADSI Edit
C. The csvde.exe command
D. Active Directory Users and Computers
Answer: C
Explanation:
Csvde.exe is the best option to add multiple users. as you just need to export the excel spreadsheet as a csvfile and make sure the parameters are correct.
You can use Csvde to import and export Active Directory data that uses the commaseparated valueformat. Use a spreadsheet program such as Microsoft Excel to open this .csv file and view the header andvalue information.
http://support.microsoft.com/kb/327620/en-us
QUESTION 162
Your network contains two subnets. The subnets are configured as shown in the following table.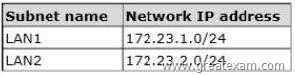
You have a server named Server2 that runs Windows Server 2012 R2. Server2 is connected to LAN1.
You run the route print command as shown in the exhibit. (Click the Exhibit button.)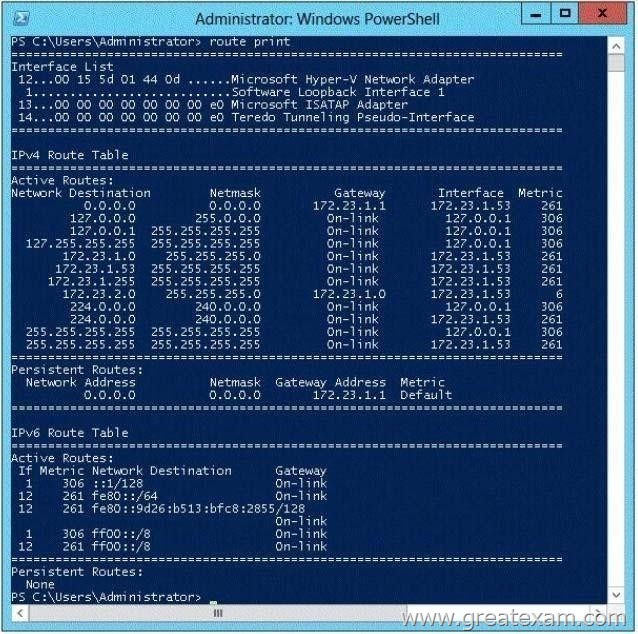
You need to ensure that Server2 can communicate with the client computers on LAN2.
What should you do?
A. Change the metric of the 10.10.1.0 route.
B. Set the state of the Teredo interface to disable.
C. Set the state of the Microsoft ISATAP Adapter #2 interface to disable.
D. Run route delete 172.23.2.0.
Answer: D
Explanation:
Route is used to view and modify the IP routing table.
Route Print displays a list of current routes that the host knows.
Default gateways are important to make IP routing work efficiently.
TCP/IP hosts rely on default gateways for most of their communication needs with hosts on remote
network segments. In this way, individual hosts are freed of the burden of having to maintain extensive and continuously updated knowledge about individual remote IP network segments. Only the router that acts as the default gateway needs to maintain this level of routing knowledge to reach other remote network segments in the larger internetwork.
If the default gateway fails, communication beyond the local network segment may be impaired. To prevent this, you can use the Advanced TCP/IP Settings dialog box (in Network Connections) for each connection to specify multiple default gateways. You can also use the route command to manually add routes to the routing table for heavily used hosts or networks.
If you have multiple interfaces and you configure a default gateway for each interface, TCP/IP by default automatically calculates an interface metric that is based on the speed of the interface. The interface metric becomes the metric of the default route in the routing table for the configured default gateway. The interface with the highest speed has the lowest metric for its default route. The result is that whenever multiple default gateways are configured on multiple interfaces, the fastest interface will be used to forward traffic to its default gateway.
If multiple interfaces of the same speed have the same lowest interface metric, then, based upon the binding order, the default gateway of the first network adapter is used. The default gateway for the second network adapter is used when the first is unavailable.
In order for Host A on Network 1 to communicate with Host B on Network 2, Host A first checks its routing table to see if a specific route to Host B exists. If there is no specific route to Host B, Host A forwards its TCP/IP traffic for Host B to its own default gateway, IP Router 1.
http://technet.microsoft.com/en-us/library/cc779696%28v=ws.10%29.aspx
http://technet.microsoft.com/en-us/library/cc958877.aspx
http://support.microsoft.com/kb/299540/en-us
QUESTION 163
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server1.
Server1 runs Windows Server 2012 R2 and has the Hyper-V server role installed.
You need to log the amount of system resources used by each virtual machine.
What should you do?
A. From Windows PowerShell, run the Enable-VMRe5ourceMetering cmdlet.
B. From Windows System Resource Manager, enable Accounting.
C. From Windows System Resource Manager, add a resource allocation policy.
D. From Windows PowerShell, run the Measure-VM cmdlet.
Answer: A
Explanation:
Route is used to view and modify the IP routing table.
Route Print displays a list of current routes that the host knows. Default gateways are important to make IP routing work efficiently. TCP/IP hosts rely on default gateways for most of their communication needs with hosts on remote networksegments. In this way, individual hosts are freed of the burden of having to maintain extensive andcontinuously updated knowledge about individual remote IP network segments. Only the router that acts as thedefault gateway needs to maintain this level of routing knowledge to reach other remote network segments inthe larger internetwork. If the default gateway fails, communication beyond the local network segment may be impaired. To preventthis, you can use the Advanced TCP/IP Settings dialog box (in Network Connections) for each connection tospecify multiple default gateways. You can also use the route command to manually add routes to therouting table for heavily used hosts or networksIf you have multiple interfaces and you configure a default gateway for each interface, TCP/IP by
defaultautomatically calculates an interface metric that is based on the speed of the interface. The interface metricbecomes the metric of the default route in the routing table for the configured default gateway. The interfacewith the highest speed has the lowest metric for its default route. The result is that whenever multiple defaultgateways are configured on multiple interfaces, the fastest interface will be used to forward traffic to its defaultgateway.
If multiple interfaces of the same speed have the same lowest interface metric, then, based upon the bindingorder, the default gateway of the first network adapter is used. The default gateway for the second networkadapter is used when the first is unavailable. In order for Host A on Network 1 to communicate with Host B on Network 2, Host A first checks its routing tableto see if a specific route to Host B exists. If there is no specific route to Host B, Host A forwards its TCP/IPtraffic for Host B to its own default gateway, IP Router 1.
http://technet.microsoft.com/en-us/library/cc779696%28v=ws.10%29.aspx http://technet.microsoft.com/en-us/library/cc958877.aspx http://support.microsoft.com/kb/299540/en-us
QUESTION 164
You have a server named Server1 that runs Windows Server 2012 R2.
You plan to create an image of Server1.
You need to remove the source files for all server roles that are not installed on Server1.
Which tool should you use?
A. servermanagercmd.exe
B. imagex.exe
C. dism.exe
D. ocsetup.exe
Answer: C
Explanation:
servermanagercmd.exe – The ServerManagerCmd.exe command-line tool has been deprecated in WindowsServer 2008 R2. imagex.exe – ImageX is a command-line tool in Windows Vista that you can use to create and manageWindows image (.wim) files. A .wim file contains one or more volume images, disk volumes that containimages of an installed Windows operating system. dism.exe – Deployment Image Servicing and Management (DISM.exe) is a command-line tool that canbe used to service a Windows image or to prepare a Windows Preinstallation Environment (WindowsPE) image. It replaces Package Manager (Pkgmgr.exe), PEimg, and Intlcfg that were included in
Windows Vista
The functionality that was included in these tools is now consolidated in one tool(DISM.exe), and new functionality has been added to improve the experience for offline servicing. DISMcan Add, remove, and enumerate packages. ocsetup.exe – The Ocsetup.exe tool is used as a wrapper for Package Manager (Pkgmgr.exe) and for WindowsInstaller (Msiexec.exe).
Ocsetup.exe is a command-line utility that can be used to perform scripted installs andscripted uninstalls of Windows optional components. The Ocsetup.exe tool replaces the Sysocmgr.exe tool thatWindows XP and Windows Server 2003i use.
http://technet.microsoft.com/en-us/library/hh824822.aspx http://blogs.technet.com/b/joscon/archive/2010/08/26/adding-features-with-dism.aspx http://technet.microsoft.com/en-us/library/hh831809.aspx
http://technet.microsoft.com/en-us/library/hh825265.aspx
QUESTION 165
Your network contains an Active Directory domain named contoso.com.
An administrator provides you with a file that contains the information to create user accounts for 200 temporary employees. The file is shown in the exhibit. (Click the Exhibit button.)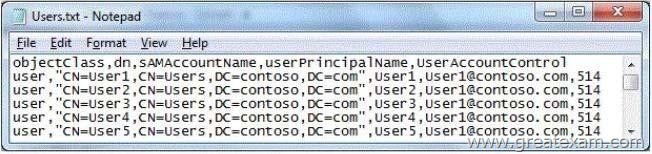
You need to automate the creation of the user accounts.
You must achieve this goal by using the minimum amount of administrative effort.
Which tool should you use?
A. csvde
B. Net user
C. Ldifde
D. Dsadd
Answer: A
Explanation:
csvde – Imports and exports data from Active Directory Domain Services (AD DS) using files thatstore data in the comma-separated value (CSV) format.
You can also support batch operations based on the CSV file format standard.
http://technet.microsoft.com/en-us/library/cc732101(v=ws.10).aspx
Net user – Adds or modifies user accounts, or displays user account information.
http:// technet.microsoft.com/en-us/library/cc771865(v=ws.10).aspx
Ldifde – Creates, modifies, and deletes directory objects. You can also use ldifde to extend the schema, export Active Directory user and group information to other applications or services, and populate Active Directory Domain Services (AD DS) with data from other directory services.
http://technet.microsoft.com/ en-us/library/cc731033(v=ws.10).aspx
Dsadd – Adds specific types of objects to the directory.
http://technet.microsoft.com/en-us/library/cc753708 (v=ws.10).aspx
csvde.exe is the best option to add multiple users. as you just need to export the excel spreadsheet as a csv file and make sure the parameters are correct.
You can use Csvde to import and export Active Directory data that uses the comma-separated value format. Use a spreadsheet program such as Microsoft Excel to open this .csv file and view the header and value information
http://support.microsoft.com/kb/327620/en-us
QUESTION 166
Hotspot Question
Your network contains an Active Directory domain named contoso.com. All client computers run Windows 8. An administrator creates an application control policy and links the policy to an organizational unit (OU) named OU1. The application control policy contains several deny rules. The deny rules apply to the Everyone group.
You need to prevent users from running the denied application.
What should you configure? To answer, select the appropriate object in the answer area.
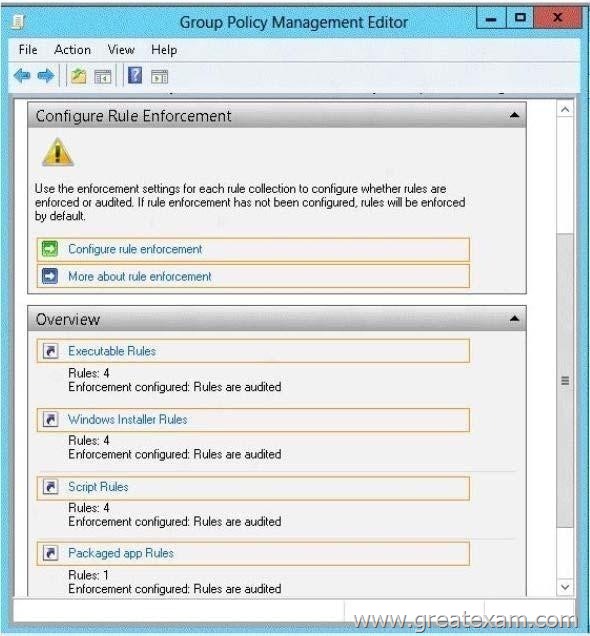
Answer: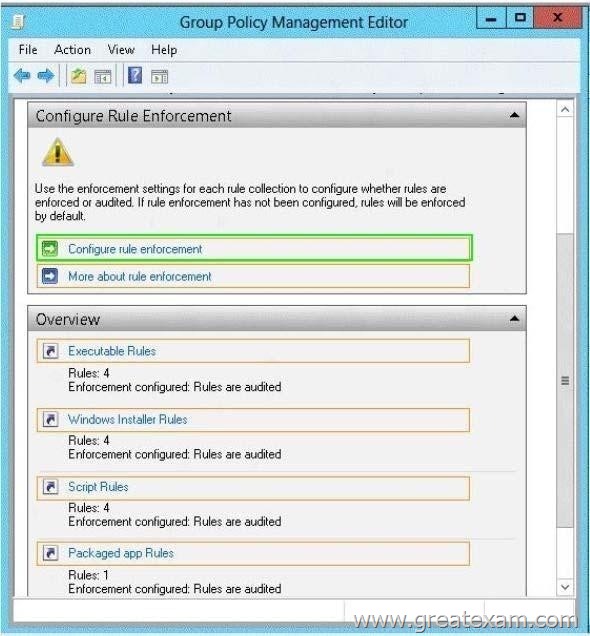
Explanation:
To enable the Enforce rules enforcement setting by using the Local Security Policy snap-in
1. Click Start, type secpol.msc in the Search programs and files box, and then press ENTER.
2. If the User Account Control dialog box appears, confirm that the action it displays is what you want, and then click Yes.
3. In the console tree, double-click Application Control Policies, right-click AppLocker, and then click Properties.
4. On the Enforcement tab, select the Configured check box for the rule collection that you want to enforce, and then verify that Enforce rules is selected in the list for that rule collection.
5. Repeat step 4 to configure the enforcement setting to Enforce rules for additional rule collections.
6. Click OK.
http://technet.microsoft.com/en-us/library/ee791885(v=ws.10).aspx
QUESTION 167
You have a print server named Server1 that runs Windows Server 2012 R2.
You discover that when there are many pending print jobs, the system drive occasionally runs out of free space.
You add a new hard disk to Server1.
You create a new NTFS volume.
You need to prevent the print jobs from consuming disk space on the system volume.
What should you modify?
A. the properties of the Print Spooler service
B. the Print Server Properties
C. the properties of each shared printer
D. the properties on the new volume
Answer: B
Explanation:
Windows spools print jobs by default to the following directory as the they are processed:
%SystemRoot%\SYSTEM32\SPOOL\PRINTERS.
It is possible for the administrator of a Windows print server to manually instruct Windows the location forplacing the spool files, if for example there is a concern for disk space.
http://support.microsoft.com/kb/137503/en-us
http://technet.microsoft.com/en-us/library/cc757764%28v=ws.10%29.aspx http://technet.microsoft.com/en-us/library/cc736979%28v=ws.10%29.aspx
QUESTION 168
Your network contains an Active Directory domain named contoso.com. The domain contains an application server named Server1. Server1 runs Windows Server 2012 R2.
You have a client application named App1 that communicates to Server1 by using dynamic TCP ports. On Server1, a technician runs the following command:
New-NetFirewallRule -DisplayName AllowDynamic -Direction Outbound -LocalPort 1024- 65535 -Protocol TCP
Users report that they can no longer connect to Server1 by using Appl.
You need to ensure that App1 can connect to Server1.
What should you run on Server1?
A. Set-NetFirewallRule -DisplayName AllowDynamic -Action Allow
B. netsh advfirewall firewall set rule name=allowdynamic new action = allow
C. Set-NetFirewallRule -DisplayName AllowDynamic -Direction Inbound
D. netsh advfirewall firewall add rule name=allowdynamic action=allow
Answer: C
Explanation:
Set-NetFirewallRule – Modifies existing firewall rules.
You have to allow the connection INTO the server – inbound rules
http://technet.microsoft.com/en-us/library/jj573828%28v=wps.620%29.aspx http://mikefrobbins.com/2013/02/28/use-powershell-to-remotely-enable-firewall-exceptionson- windows-server-2012/
QUESTION 169
You have a server named dc2.contoso.com that runs Windows Server 2012 R2 and has the DNS Server server role installed.
You open DNS Manager as shown in the exhibit. (Click the Exhibit button.)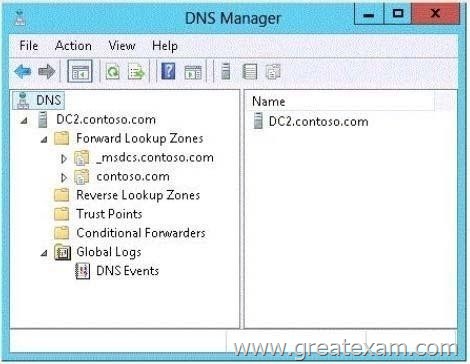
You need to view the DNS server cache from DNS Manager.
What should you do first?
A. From the View menu, click Advanced.
B. From the Action menu, click Configure a DNS Server…
C. From the View menu, click Filter…
D. From the Action menu, click Properties.
Answer: A
Explanation:
To view the contents of the DNS cache, perform the following steps:
1. Start the Microsoft Management Console (MMC) DNS snap-in (Go to Start, Programs, Administrative Tools,and click DNS).
2. From the View menu, select Advanced.
3. Select the Cached Lookups tree node from the left-hand pane to display the top-level domains (e.g., com, net) under.(root). Expand any of these domains to view the cached DNS information (the actual records willappear in the right-hand pane).
QUESTION 170
You work as an administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers on the L2P.com network have Windows Server 2012 R2 installed.
L2P.com has a server, named L2P-SR07, which has two physical disks installed. The C: drive hosts the boot partition, while the D: drive is not being used. Both disks are online.
You have received instructions to create a virtual machine on L2P-SR07.
Subsequent to creating the virtual machine, you have to connect the D: drive to the virtual machine.
Which of the following is TRUE with regards to connecting a physical disk to a virtual machine?
A. The physical disk should not be online.
B. The physical disk should be uninstalled and re-installed.
C. The physical disk should be configured as a striped disk.
D. The physical disk should be configured as a mirrored disk.
Answer: A
Explanation:
Your virtual machines can also be connected to physical hard disks on the virtualization server virtual hard disks. (This is sometimes referred to as having a “pass-through” disk connected to a virtual machine.)
The physical hard disk that you connect to a virtual machine can also be a network-attached disk, like a logical unit number (LUN) in a storage area network (SAN). A common example is an iSCSI LUN that has been mapped to the virtualization server by using Microsoft iSCSI Initiator. Because the virtualization server sees network-attached storage as local disks, the iSCSI LUN can be connected to a virtual machine.
The most important limitation about having a physical hard disk connected to a virtual machine is that it cannot be connected to the virtualization server or to other virtual machines at the same time. The virtual machine must have exclusive access to the physical hard disk.
Pass-through Disk Configuration
Hyper-V allows virtual machines to access storage mapped directly to the Hyper-V server without requiring the volume be configured. The storage can either be a physical disk internal to the Hyper-V server or it can be a Storage Area Network (SAN) Logical Unit (LUN) mapped to the Hyper-V server. To ensure the Guest has exclusive access to the storage, it must be placed in an Offline state from the Hyper-Vserver perspective
http://blogs.technet.com/b/askcore/archive/2008/10/24/configuring-pass-through-disks-in-hyper-v.aspx
http://technet.microsoft.com/pt-pt/library/ff404147%28v=ws.10%29.aspx
You can pass Microsoft 70-410 exam if you get a complete hold of 70-410 braindumps in GreatExam. What’s more, all the 70-410 Certification exam Q and As provided by GreatExam are the latest.